A bonus second post for the week this time around, mainly because I had some extra time to study and this is only going to be a short post briefly covering a couple of traffic capture tools. This is because I have tried to keep my study as specific to the OSCP exam as possible at this stage, before going back and expanding on areas I feel weaker at or am specifically interested in.
With that said, capturing traffic is another useful way to gather information from another machine on a local network. This assumes you have access to the internal network, which may be the case in certain penetration testing contexts to simulate an insider threat or to assess the damage an attacker can do post breach. As usual, there are a range of tools that have been developed which can capture traffic for us in relatively easy to use ways. The two tools I focused on are specifically the most relevant to the OSCP exam: Wireshark and tcpdump.
Wireshark
Wireshark is a graphical network protocol analyzer which can capture the individual packets moving around the network. Wireshark is robust in the sense that it can capture almost all traffic types, but is also simple in the sense that it has an easy to use graphical interface and an intuitive design.
I configured the settings on wireshark and began capturing packets that went to and from my Kali Linux machine. To test, I did a very basic ping command to my Ubuntu machine to see if this traffic would be captured. Sure enough, after setting a filter to show information relevant only to my Ubuntu machine, I was able to see the ping requests and information about each one.
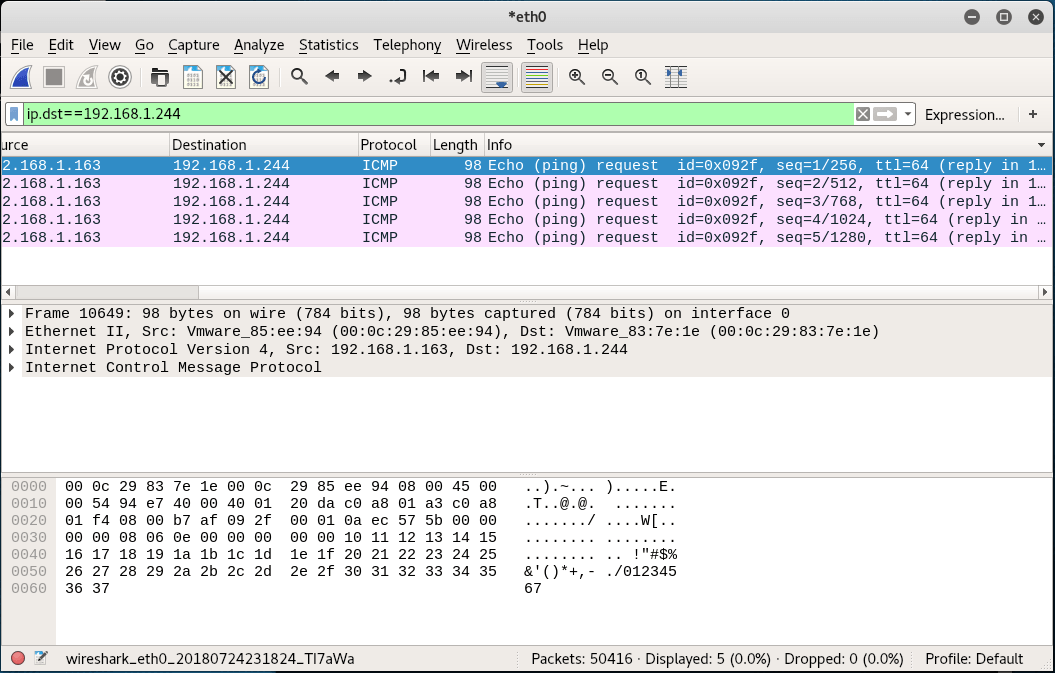
The output view of the Wireshark scan. Note the Info column detailing the ping requests.
In other examples of Wireshark I studied, people were able to pick up pretty much everything down to the detail of individual keystrokes. It is not hard to see how Wireshark could be used to find user credentials and other sensitive information.
tcpdump
This is another traffic capture tool, however it is based on the command line unlike Wireshark. Tcpdump works similarly to other command line tools I have used in the past, with an extensive list of options to refine the search and filter the output. I’ll be honest and say I don’t fully understand how to use this tool yet, so I will surely have to revisit this in the future.
A good guide on tcpdump with examples and information about various settings can be found here:
https://www.giac.org/paper/gsec/3489/beginners-guide-tcpdump/105700
Conclusion
Capturing traffic can be very powerful, given the right parameters are set to refine the output. If this is not done, the output will likely be far too extensive to efficiently provide any value. However, when done correctly, the captured traffic could potentially outright give tell you usernames and passwords, or at the very least provide some information to assist with an exploit.
I’m expect that I will be able to understand the outputs of what I am capturing in greater detail with more practice, because at the moment I can understand only the obvious pieces of information. I’m still very new to penetration testing, and whilst I am learning a lot there is still a long way for me to go!
–Kento