This post is a direct follow up to the previous one, and is also considered part of the Enumeration phase of penetration testing.
After gathering general information, the next step is to start searching for vulnerabilities that might exist on a system. Any potential vulnerabilities are then noted down to provide a starting point for the exploitation phase of a penetration test.
It has become apparent to me as I study penetration testing that if a task requiring manual input exists, an automated tool for that task will also exist. Unsurprisingly, vulnerability scanning is no exception to this rule.
The most widely used vulnerability scanner is Nessus. Although this tool has a wide range of features to make vulnerability scanning extremely convenient, I decided against learning about it in any great detail. The reason for this simply boils down to the OSCP exam not allowing the use of Nessus or other similar tools. Instead, the OSCP exam focuses more on the manual vulnerability scanning to force students into a greater level of understanding about the ways to search for and identify vulnerabilities. So although the automated tool does exist, I won’t be using one for the time being (despite how much easier it would make my things!)
Nmap Scripting Engine
Enter our old pal Nmap! Having progressively acquired more features over the course of its development, Nmap can now run public scripts to scan for vulnerabilities in addition to its port mapping capabilities.
Nmap contains an extensive range of scripts that are available for use, and also features help commands if you ever require more in depth information.
For example, the nfs-ls.nse script help page shows information about what the script is searching for and achieving.
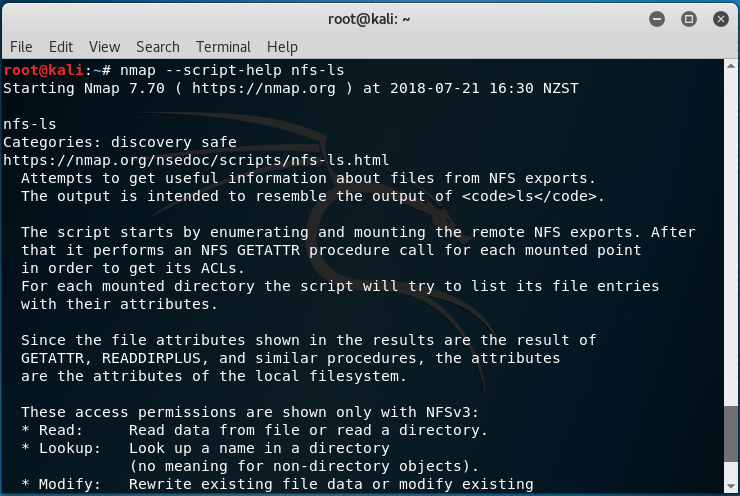
The help page for nfs-ls. From this we can see that the script mounts the remote NFS exports and gathers information about the mounted port. Finally, it will list information about the the file entries.
running the nfs-ls script against the Linux machine brought up some interesting information, particularly about the SSH directory. The SSH directory may include sensitive information such as SSH keys or a list of authorized keys, which can be used for authentication to gain access.
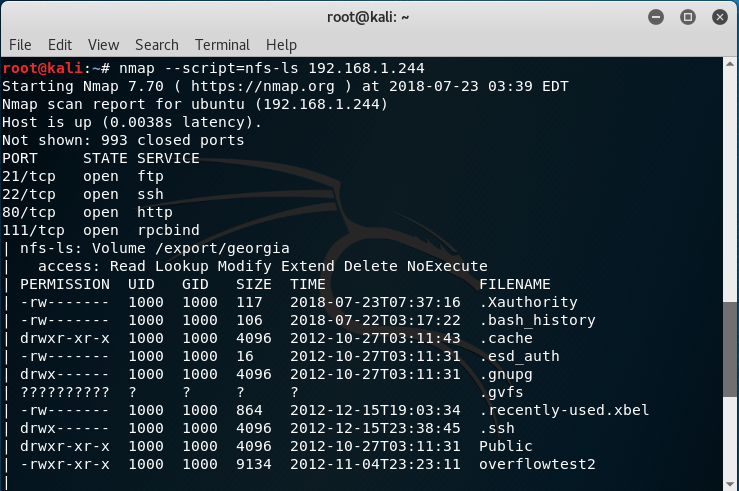
Output of an Nmap nfs-ls script scan. Of particular note here is the .ssh directory which may be exploitable
The Nmap script therefore found a potential vulnerability in the Linux machine which could be used to gain admin access.
I also learned that some Nmap Scripting Engine scripts may crash services or otherwise cause unwanted damage to the system. It is therefore important to remember to always check the help information of each script for potential danger levels and avoid being too reckless with the scripts I choose to run.
Metasploit
Enter our old pal Metasploit! Although very basic, Metasploit does offer a way to scan for vulnerabilities without actually executing an exploit. The check function can be used to connect to a target and check if it is vulnerable, acting as a basic type of vulnerability scan.
However, not all modules have this function available, so there are limitations with this method of vulnerability scanning.
Nikto
Nikto is another scanning tool that looks specifically for dangerous files, outdated versions and misconfigurations. Essentially Nikto runs a scan against every application with a set of known vulnerabilities to find anything of value. Running the scan against the Linux machine, I found that a vulnerable version of the TikiWiki software installed on the machine, which may allow the execution of PHP code.
Further researching the code for this vulnerability, OSVDB-40478 links to an exploit contained withing Metasploit that can be executed during the exploitation phase.
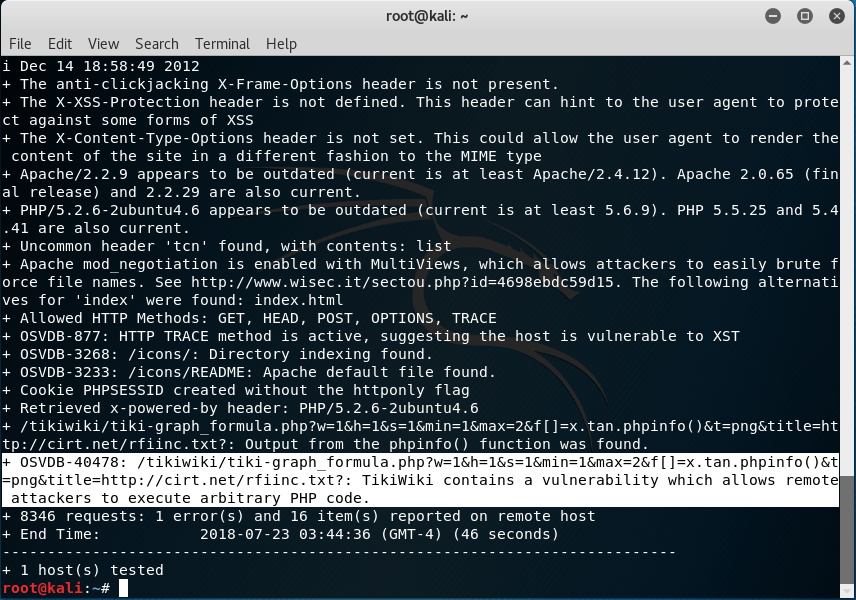
Note the highlighted area, but also the other information gathered above that may also be vulnerabilities that can be exploited.
Other tools
Other tools that I briefly explored were enum4linux and SPARTA. Both of these are downloaded tools which also scan various systems for vulnerabilities but provide enhanced features usability, such as a GUI for example. I found these to be of similar value to the Nmap Scripting Engine, so will not cover them in too much detail here.
Manual Analysis – Ports
Occasionally, a port may crash when Nmap scans it, because it expects only a certain type of input. These ports can be manually scanned by connecting to them with a web browser and using netcat to make the retrieve more specific information without causing the port to crash.
The information that can be obtained using this more manual, individual method can then be searched further to determine if it is exploitable.
Manual Analysis – Usernams
There are a few techniques that Georgia touches upon in her book that can be used to obtain a valid username. This makes password attacks much more efficient, as knowing the username part of a credentialed login means only the password needs to be cracked. This is an area that will be expanded upon later, but an example was given that used the VRFY SMTP command to find usernames for mail servers.
Conclusion
I felt a bit more comfortable with what I was doing in the larger picture, compared to when I was simply gathering whatever information I could find. Part of that is the names of vulnerabilities either had descriptions already, or could be Googled to learn more about them and the potential exploit opportunities they provide.
I also realized how time consuming the Enumeration phase can be, but also how important it is to get things right. In order for an exploit to be successful, all the information and vulnerabilities must be found with extreme detail. This is done to ensure the success of the exploitation and to prevent undesired crashes or damage to a system.
Continuing on from the information gathering theme, I’ll be moving onto traffic capture next to learn about monitoring tools and what value they can provide.