Backtracking a little bit from the Metasploit framework I covered last week, I decided to spend a significant amount of time on information gathering, otherwise known as Enumeration.
There are plenty of methods you can use to find out information, with some pieces of information more valuable than others. Nevertheless, it is important to take due diligence and carefully utilize all tools and collect as much information as possible. After all, it won’t matter if you know how to run exploits, if you don’t know what to exploit.
Open Source Intelligence Gathering
This seemed like a logical starting point. Open source information is gathered entirely from legal sources such as public records or social media pages. This means that information collected through these methods are out in the public domain, and there are no legal implications involved in searching for these pieces of information.
Some of the tools used in Open Source Intelligence Gathering are:
- Netcraft.com – this is a company that allows you to query another website to display information about it such as IP address, Age, Hosting company, Web Server Type and Hosting Country.
- Whois lookup – this is run via the linux command line and primarily provides domain record information. Occasionally, this can also provide more information such as phone numbers or email addresses.
- Nslookup – can provide more specific search queries such as mail server type. This can be done by setting the type of search to further filter the output of the query. For example, set type=mx will set the type to email
- Host – another DNS utility, -t ns domain can be used to find the name servers available. This information can be further used to find zone transfers, which in turn can identify vulnerabilities
Email gathering
Finding email addresses available on the internet is actually very easy to do with the correct tools.
These emails can potentially be used as surrogates for usernames, and can be used to find password dumps or other information.
TheHarvester is a linux tool that queries search engines to find email addresses automatically. Using the command theharvester -d bulbsecurity.com -l 500 -b all searches the first 500 results in all search engines for bulbsecurity.com
TheHarvester lists out the options clearly, but for the sake of my future reference I will list down what each of the letters mean:
- -d: The domain to search or company name
- -l x: Limit the number of results to x
- -b: the data source. -b all searches all the possible search engines including LinkedIn and Twitter.
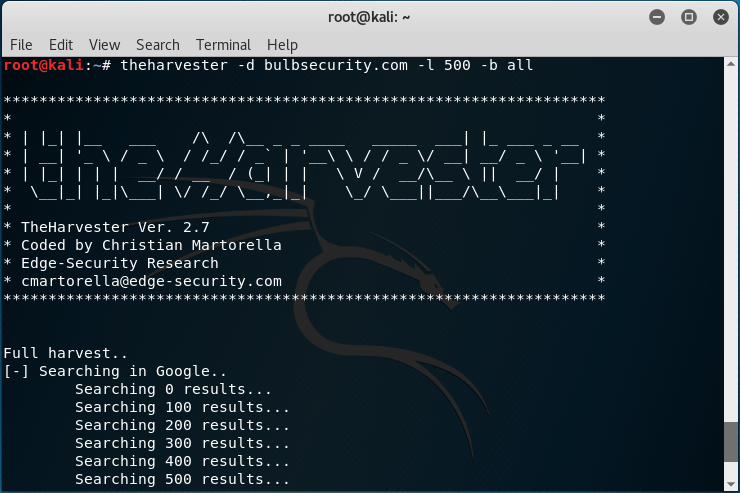
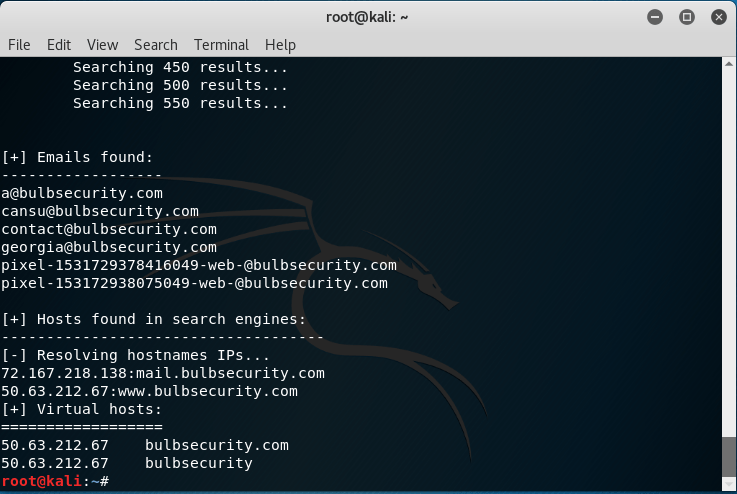
TheHarvester main screen and output of the bulbsecurity.com search. A few email addresses were found including georgia@bulbsecurity.net as well as some of the other websites shared with virtual hosting.
I ran TheHarvester against my own site kentosec.wordpress.com, to see what it would pick up out of curiosity. To my surprise, it wasn’t able to find my personal email address! I guess this means WordPress is doing a decent job at protecting client email addresses, something I’ll be sure to test more of further on.
Port Scanning
When looking at what ports are open and running, Netcat and telnet are two commands that can be used to manually check for ports. However, doing a single port scan of potentially thousands will take a significant amount of time, so the tool Nmap can be used to find all listening ports automatically.
I had actually used Nmap previously to troubleshoot some of the connection issues I was having with my Windows XP machine, so was already familiar with some of the features and expected outputs.
Still, it was worthwhile learning about the various types of scan Nmap can use and in what situations you would use them.
- SYN scan – Nmap sends a SYN and waits for the SYN-ACK response if the port is open, however Nmap will not send the final ACK response. Therefore, the connection is never properly established. Syntax: -sS
- Version scan – Nmap completes the connection and then attempts to determine what software is running and the version of that software. This provides more information that the SYN scan, although it is potentially detectable as a full connection is being made. Syntax: -sV
- UDP scan – this Nmap scan specifically targets UDP ports, as opposed to the previous scans which targeted TCP ports. This is done by sending a UDP packet and tracks the response – ports that do not respond are not UDP ports. Syntax: -sU
- Nmap scans the ‘most interesting’ 1000 ports, but specific ports can be targeted manually also. This may be useful in case the previous scans missed a few ports that are of particular interest. Syntax: -p
It has become clear that searching for information is the easy part, but knowing what the information means is much more difficult. A lot of the outputs of these searches were difficult to understand and it took me some time to study each one before I fully understood the information it was providing. Even then, I was still relatively clueless as to what the outputs meant from a exploit perspective.
Just goes to show I still have a lot to learn 🙂
Kento