So the title basically gives the crux of this post away. My OSCP course start date has been confirmed for October 21st! After months of preparation, I’ll finally be starting the OSCP PwK course exactly a week from today. I’m extremely excited at the prospect of getting stuck in with both the course and lab content to learn all that it has to offer.
So how will I be spending these last moments in preparation for the PwK? By taking a break. I know that I will be spending a tonne of hours on the OSCP course once I start and to avoid burnout, I decided to take it easy and mentally recharge and prepare myself. In some respects, this is the calm before the OSCP storm.
I’m not entirely going to be stopping all together, though. To keep myself in the penetration testing mentality I did complete the Devel box on HackTheBox, and am going through the excellent CTF – Beginner series by IppSec. This curated playlist contains his HackTheBox walkthroughs that he feels are useful for beginners and totals 11 videos. Going through 1 of these videos a day will be a good way to unwind whilst still learning new things and staying sharp.
Next week will be my final blog post before I officially start the OSCP course. I will review the preparation work I’ve done so far, analyse my strengths and weaknesses and discuss my expectations for the OSCP course.
See you next week!
Kento.
Devel
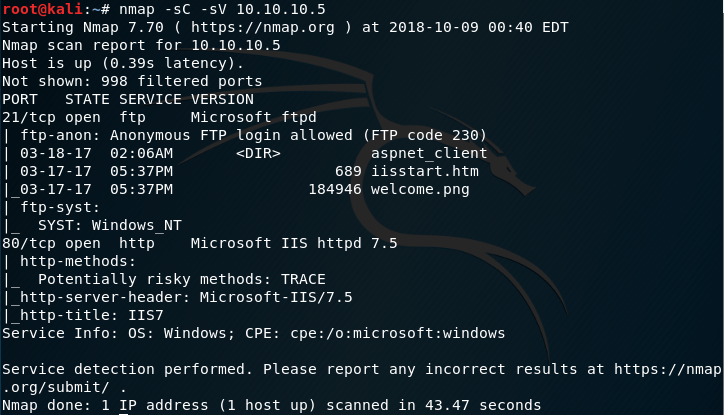
Starting with an Nmap scan, we can see that ftp is enabled. I know from past experience that ftp is often vulnerable and so I decided this would be a good place to start.
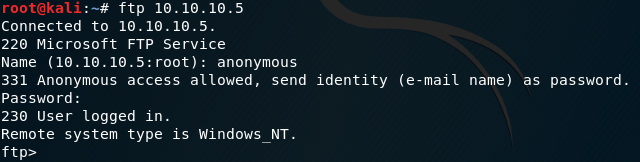
After making a connection to the ftp server, I was not surprised to find that anonymous connections were allowed. After all, the default scripts I ran in nmap said they would be.

Using msfvenom, I created a reverce_tcp payload and saved it as a .aspx file.

This was then uploaded to the ftp server using the put command.


Browsing to the file uploaded with a multi handler module running in metasploit, we receive a meterpreter session.

Using the local exploit suggester module in metasploit, I found the ms10_015 kitrap0d module that was
suggested to be effective in this situation.


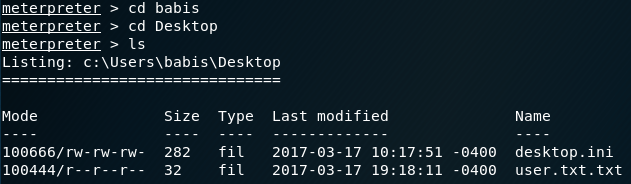

The module runs, and we successfully escalate privileges to the system level. This allows us to browse to the user and administrator directories to capture our flags!