After setting up my virtual labs, I decided to go back and read Chapter 0 of Gerogia’s book titled Penetration Testing Primer. Although I already had a fairly good understanding of the penetration testing basics, I figured extra revision wouldn’t hurt.
The primer chapter covered the different types of penetration tests, as well as the stages of a penetration test. The stages of a penetration test were covered in more detail than I had previously learned, they include:
- Pre-engagement
- Information-gathering
- Threat-modeling
- Vulnerability analysis
- Exploitation
- Post-exploitation
- Reporting
The chapter was understandably brief, as many of these concepts will be covered at later stages of the book.
Linux Basics
Linux is an operating system that I was previously unfamiliar with. With powerful functions executed on the command line, I had to learn all the basic commands and how they interact with each other.
I will list the commands I learned below, each with very brief summaries of their functions.
Standard Functions

ls – view contents of the directory
pwd – print the current directory
cd – change directory
man – manual page, learn more about a certain command
adduser – adding a new user
adduser sudo – add a user to the sudo group. This is a group which can request root privileges
A view of some standard functions including adding a new user to the sudo group
File Functions
 touch myfile – create a new, empty
touch myfile – create a new, empty
file cp – copy a file
mv – move a file
-r – remove a file
echo – echos what you enter into terminal
> – write to a file
cat – see the contents of a file
>> – append text to a file
using echo and cat to view and edit a file
File Permissions
ls -l – view the permissions
(r) read, write, (x) execute
first 3 for owner
next three are for owner, group, users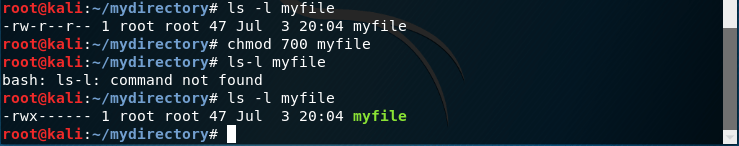 chmod – change the permissions
chmod – change the permissions
File Editors
vi – A text editor. This text editor features two different modes, command and insert mode. There are different functions within vi to provide functions, but they are not visible on the screen. For example, the command ‘dd’ deletes a whole line
nano – Another text editor. This one is much forgiving and works in a similar way to standard text editors, with commands at the bottom that provide further functions.


A view of the two different text editors. Vi on the left, nano on the right
Data Manipulation
 grep – looks for instances of a text string in a file
grep – looks for instances of a text string in a file
pipe (|) and cut – to alter the output of grep
sed – editing files based on patterns or expressions

awk – another utility for pattern matching
apt-get – can be used to install packages not pre installed but contained within the repositories.

Viewing the IP, Gateway and Default information to use with netstat and netcat

netstat – displays the network connections for the Transmission Control Protocol
![]()
netcat – utility for reading and writing to network connections using TCP or UDP. Netcat is knows as the “Swiss Army Knife” of network connections as it has many functions.

Note how the information entered into the smaller terminal was mirrored on the larger. Although basic, it is clear how this technique could be used in penetration testing.

copy a file over a network using input/output
> – output
< – input

Crontab – list of automated jobs. Can be added to based on hourly, daily, weekly, monthly
Scripting and Programming Basics
Moving on from the linux commands, I started on the basics of scripting and programming. Thankfully I already had some background in these areas with various languages, so the prospect of code was not too daunting. Bash, Python and C were covered in brief detail.
Bash Scripting
Bash scripts are files that run terminal commands. This means that any command that can be run in the terminal window can also be executed via a bash script.
I first created a simple bash script to ping hosts on the network. Using nano to edit the file pingscript.sh, I was able to create a script that would ping an IP address and cycle through the final IP octet from 1 – 254. The output would therefore produce 254 results sequentially, which saves having to enter each ping manually.


The first iteration of pingscript.sh (output on the left) – the results required further streamlining…

Refined the output to create a less confusing display of information. This was done by using the commands covered earlier, including grep, cut and sed.
Python Scripting
Next I went and created a basic Python script, which prompts the user for an IP address and port number. The return will then inform the user whether that port is open or closed.
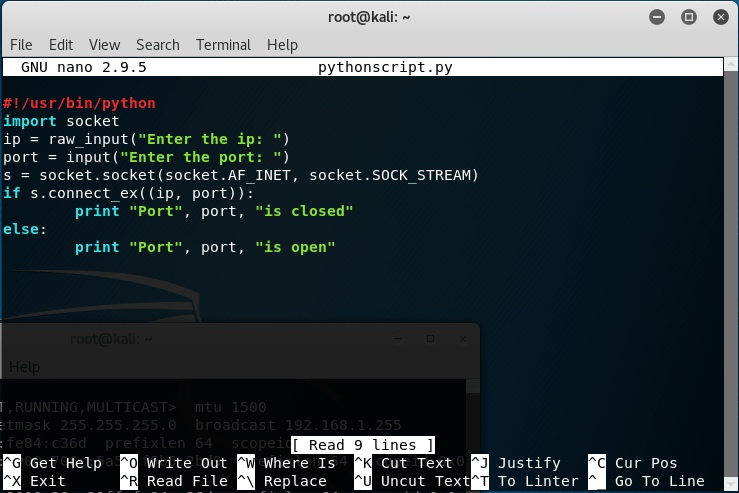
The if statement here alongside print is what returns the output of ‘closed’ or ‘open’
C Scripting and Compling
Finally, I wrote a basic C program and compiled it into a language that can be understood and executed by Kali Linux.
The program simply prints ‘hello’ and the name of the user when passed as an argument on the command line. Again, this was a simple program but served the purpose of introducing C programming and compiling from within the terminal window.


Concluding Thoughts
There was a lot to unpack in this crash course of basic concepts and functions. Although I by no means feel like an expert on any of the content covered in this blog post, I am confident that I will be able to understand them later on as the complexity increases.
Next week I’ll be moving onto the Metasploit framework, which I am looking forward to. This is a core penetration testing tool so I am hoping to learn about it with sufficient detail before moving on.
Also, apologies if the layout of this post was confusing, particularly the screenshots. I am still experimenting with different layout styles to see which ways work the best.
– Kento.
I got what you mean ,saved to favorites, very nice website .
LikeLike
Greetings! Quick question that’s completely off topic. Do you know how to make your site mobile friendly? My blog looks weird when browsing from my iphone 4. I’m trying to find a theme or plugin that might be able to resolve this problem. If you have any recommendations, please share. Appreciate it!
LikeLike