After a few weeks of set-up and familiarizing myself with the basics, this week I began to do what felt like some actual penetration testing. Although I do not feel as though these previous weeks were in vain, I’ll admit that it at times it has been a grind to get through. I was therefore extremely excited to get stuck in with some basic exploitation using the Metasploit framework.
Metasploit is a tool that is pre-loaded in Kali Linux, and provides a platform to develop new exploits as well as a library for existing . This makes Metasploit invaluable to Information Security professionals as a knowledge base, whilst also being simple to use and understand. Metasploit is also considered trustworthy due to a community-driven vetting process all code must go through before being implemented.
I’ve seen online that the OSCP exam limits the amount of Metasploit you can use, but I still saw the value in learning the basics as a starting point for vulnerability exploitation. More than anything though, I was keen to get my hands wet with a basic exploit that would give me a basic sense of ‘hacking’ and move away from some of the basic theory and foundation content I had been covering.
Starting up Metasploit was relatively straightforward and the ASCII art that greeted me was particularly entertaining.
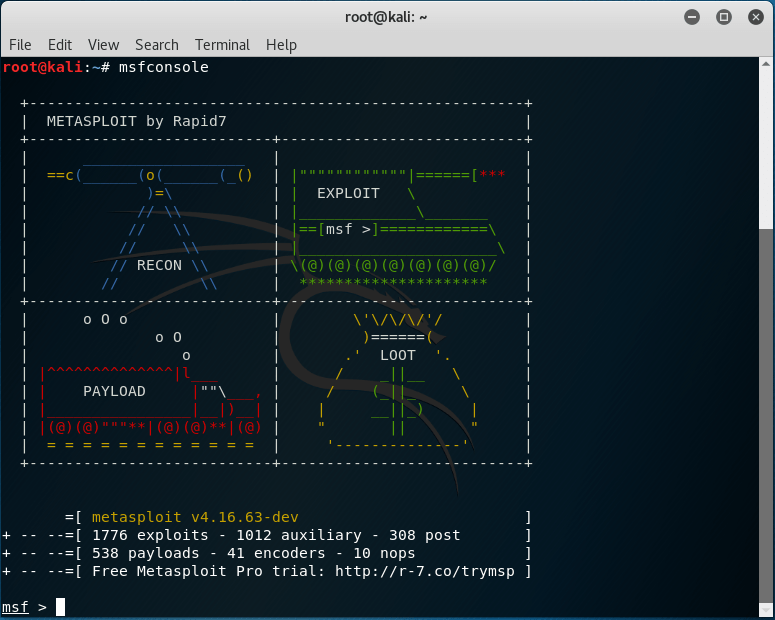
Metasploit’s msfconsole page. The latest version contains 1776 exploits!
The vulnerability I decided to exploit is known as the MS08-067 exploit for Windows XP. The unpatched Windows XP operating systems are missing the MS08-067 security bulletin, which is an opportunity to gain shell access via Meterpreter.
I honestly found this exploit fairly easy to navigate. Metasploit is straightforward in what options are available and what parameters required to run a penetration test. The only real issues I had were opening the Windows XP ports for Metasploit to connect to, as well as a minor static IP collision with another device on my local network. However, once those were corrected running the ‘exploit’ command and opening a Meterpreter session was only a formality. My first exploit was successful, and much easier than I had anticipated it would be!
Conclusion
I had a lot of fun learning about the MS08-067 vulnerability and exploiting it, and the satisfaction of gaining remote access through a Meterpreter session was the icing on the cake. However, it is important I stay aware that the work I did with Metasploit does not mean I understand the vulnerability and how it is being exported itself, merely that I was able to do so through the use of the Metasploit framework. I’m hoping that further down the line I will be able to move away from being a simple script kiddie, and understand the technical aspects of these exploits in much greater detail.
With havin so much content do you ever run into any problems of plagorism or copyright violation? My site has a lot of exclusive content I’ve either created myself or outsourced but it appears a lot of it is popping it up all over the web without my permission. Do you know any techniques to help prevent content from being stolen? I’d certainly appreciate it.
LikeLike